A bold claim by a privacy advocate or simply an attention-grabbing headline? Well, I confess, a bit of both!
In this blog we normally write about the effect of GDPR on companies, and the implications for their data-subjects. Today I’d like to focus on what data-subjects should be doing for themselves when on-line.
Last week we were at the ExecLN conference about privacy and security. One of the more intriguing presentations was about how much of your data is already out there.
A company specialising in tracking the ‘dark web’ – or rather, those bits of it they can see, which by its very nature isn’t everything, but it’s still the bits that Google can’t or doesn’t – demonstrated that of 150 security professional present at the last show, 145 of them had a footprint of some description in the unsavoury parts of the internet.
That’s right: 96% of people who ‘should know better’ had data that was for sale in the seedy side of town. I wonder what that figure is for the general population? (I feel safe in assuming that it isn’t going to be lower).
This isn’t to say GDPR has failed, I think we can conclude that awareness of privacy and risk has certainly been raised. But it would appear that the stable door is being firmly shut that little bit too late. Hopefully other horses will stay put for longer, but vast numbers are already gone.
So: what are the implications for you and me – and what can we / should we do about it?
Let’s pick one area that we can certainly improve: passwords.
Many of you may have recently received a blackmail email (as has my wife) saying “I know all about you – and to prove it here’s a password of yours. Send me bitcoin or I’ll tell everyone about your unsavoury habits”. Fortunately, Mrs W doesn’t have unsavoury online habits! But it was concerning – how had they got to this?
Well, it was a (very) old password, probably found in one of the multi-multi- data losses from Experian or others. But unnerving to say the least.
The main point here is: Someone, somewhere has at least one of your passwords. Accept it. And if that has been compromised, what else can be cracked? Different sites NEED different passwords. No ifs, no buts.
As for using the same password at work and at home… that’s even worse. Please don’t do it.
(And don’t think you can get away with just adding different numbers to a ‘root’ – the bad guys are cracking those too, running multiple variants against multiple sites).
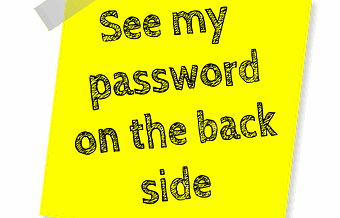
Of course, with different passwords for each site, I need a “password safe” to store all these. I currently have 195 passwords. I simply cannot remember those, and nor can you, so you need a way to record them, and that isn’t writing them on post-it notes.
But if I have to look them up each time, then I might as well make them tricky. My password safe (there are many on the market, I’m not going to pick one over the others) can generate complex and random passwords each time, so why not use those?
The obsessive may take that ‘random’ and add their own 6 characters to it… in case the generating algorithm gets cracked. It certainly adds a personal touch.
But don’t forget that the password to the ‘Password Safe’ must be highly complex AND memorable (forget it and lose the lot..). Just don’t use it anywhere else. Ever.
I use a memorable phrase – as a starting point and build on it. Simple example: Why did the chicken cross the road? To get to the other side! Wdtcxtr?2gttos! (This ISN’T my password – or root – by the way. But you get the idea…)
The other security feature to consider is 2 Factor Authentication, often written 2FA. In it’s simplest form, it means using 2 things to prove you are who you say you are. Generally these can be classed as “something you know, something you are, something you have”
So for example you type in your password (something you know) , a company sends a one-off code to a 2nd device of yours such as a phone (something you have). A troll sitting under his bridge in wherever won’t get that code, and will be foiled even if they have your password.
Many sites offer this service, and I am a big fan. OK, it might slow you down a little, but better that than your bank account being emptied. Mix it with complex passwords, and you’re signficantly better off than others.
Will unique, complex passwords, a password safe and 2FA make you perfectly secure? Honestly? No, nothing can guarantee that. But as the old adage has it, when running from a lion, you don’t need to outrun the lion, just the other guys with you.
So back to the headline: GDPR won’t protect your data, or stop it getting out there (though it might slow it down). In fact, it is best to assume and behave as if it is already publicly available. But to stop crooks taking most advantage of it?
Sort your passwords out.
NOV
2018

About the Author:
With over 30 years’ experience in the IT sector, Jim is ideally placed to lead and support initiatives in data handling and data security. He is both a Certified DPO (IBITGQ 1000104) and qualified GDPR Practitioner (IBITGQ 982862). As well as data privacy, he is very happy to talk about travelling, cycling, skiing or basketball. But it's mainly privacy.